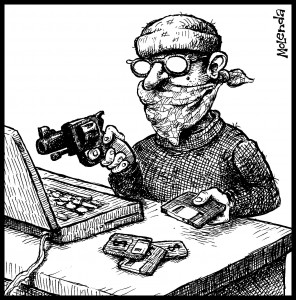
This is a true cybercrime story, which hit my friend Tom. Click here to read the whole story. Or use this page to read only chapter 1.
Preface
This is a true cybercrime story, which hit my friend Tom this past weekend… a little too close to home. And I realized that this is something that could happen to me. Indeed, it could happen to any of us who owns his own business or website domain. Tom wanted this story told, in the hopes that the knowledge will help prevent similar crimes in the future, to encourage other victims also to come forward, and to increase the chances that crimes like this will be prosecuted as a result, and I agree.
I’ve drawn on chat transcripts, emails, and other forensic evidence, to reconstruct the timeline of events as accurately as I can. Naturally, when I portray the villain’s activities—and especially his thoughts and motivations—I’m speculating… but let’s call it “informed speculation.” The villain, although he may sometimes appear incompetent, never acts out of random whim. His goal is not merely to poke around inside someone else’s computer and see what he can find. No. He is pursuing a goal, so he has a purpose to everything he does. And I’ve written his character from this perspective.
I’ve mentioned DreamHost, our hosting company and domain registrar, by name, in the interests of full disclosure, because I have recommended DreamHost and have published affiliate links to their service, and I no doubt will in the future. Because in the aftermath, I’m still looking for another company who would have done better, who would have prevented the break-ins that occurred here.
Chapter 1
I expected a typical lazy weekend: read a book, get ready for the Passover holiday, watch a few seasons of Mythbusters with my new Netflix Wii streaming disc. I never expected the weekend to bring me in so close to the world of high-stakes Internet crime.
As you may know, before I wrote books, I programmed software, and before that, I studied Electrical Engineering at Northeastern University. During those days, I met Tom, now one of my oldest friends. Both of us EE students, both electronics hobbyists since we were young, both hired as co-op students by the same local company. Both of us went into developing software. In the mid-1990’s, Tom registered the Internet domain VL.com for his consulting business, Venture Logic. Shortly thereafter, I started JT Software Enterprises and registered JTSE.com. You can’t get 2- and 3- and 4-letter domain names anymore. But at the time, the Internet was still an open frontier, and we actually homesteaded these domains, building them from the ground up.
Fast-forward to the year 2010. JTSE.com is still just an arbitrary string of characters to most people. But VL.com could stand for almost any company name, and on the open market, it’s worth hundreds of thousands of dollars. (I wonder how much Barnes and Noble paid for BN.com.)
When Tom started getting genuine offers to buy his domain, we should have realized that it was like a diamond necklace, and that high-tech cat burglars would soon set their sites on it.
Saturday, March 27, 9:17 PM EDT
A dark figure lurked in the shadows, just outside the glow of the computer monitor. No one knew him. No one even knew he was there. He had been observing his prey, quietly collecting information using false names and stolen ID’s, and even trial-and-error. Over the Internet, no one could tell he wasn’t who or what he said he was. And by the time they put together all the pieces—if they ever put together the pieces—he would be long gone, with his quarry, having taken on yet another false identity.
He knew the VL.com domain he wanted was registered with DreamHost; that was a matter of public record. And he knew that DreamHost would have limited resources to deal with a low-profile Internet break-in, especially on the weekend, and that could give him more time. He had also managed to crack into a different DreamHost account. He had asked them to add a credit card to the account, then talked to a different person and used the credit card information to validate that he owned the account. Customer service was always anxious to shortcut security in order to aid a helpless user, and he played the part like a pro. Through a long series of subterfuges, he had also discovered the account under which the domain was held, had even tricked DreamHost into linking it with his current persona. And now he was ready to strike at his true target.
“How may I assist you?” asked Dan, the support technician on the other end of the online chat.
“I having trouble with updating primary email address on my account,” the dark figure replied, impersonating his last victim. He then explained to Dan how he had tried to change the email address on the VL.com account. The story was a complete fabrication, of course; he didn’t even have access to that account. But he made sure he sneaked in the name of the account and the email address he wanted to use. He then complained that his computer was acting up, said he needed to reinstall Windows. It added an air of authentic helplessness.
Dan suggested he reset his browser, or try a different browser. A common support-guy fix.
He explained that he had already done that, and had tried Internet Explorer, Firefox, and Safari. It wasn’t important that Windows users almost never even knew about Safari; it was more important that he hit all the magic keywords, and fast, before Dan began to suspect anything.
Dan asked him to answer his security question. “What city were you born in?”
It took a minute for the dark figure to look up the correct answer, but he did find it, and answered correctly.
But Dan did not respond.
“Are you still there?” the dark figure asked.
“Changing, hold on,” Dan wrote. And finally, “Done.”
“I can see that it’s updated,” the dark figure wrote. Another fiction: he did not yet have access to the account, so he could not actually see anything. But it was important for Dan to believe that he could see it, that everything was on the up and up. It was important that no one raise an alarm, not yet.
Neither Tom nor I use such weak security questions. Anyone can find out where you were born, or what school you went to, or your mother’s maiden name, or whatever. This became painfully clear to me after I wrote my romantic memoir (Love through the Eyes of an Idiot). I looked to contact the people from my past that I wrote about, to inform them about the book. In the process of searching for them, I ran across all manner of personal information about them. I wasn’t even looking for it.
How that security question got set at DreamHost is still a mystery, lost in the memories of time. Maybe it was an old security question, set when Tom first created his account. (Be assured that we’ve both verified and tightened up security on all our accounts, and no one will be pulling a similar stunt on either of us.)
Over the following hour, Tom would receive a dozen emails from DreamHost’s computer, telling him someone was trying to reset his password. Each email included the standard calming notice:
If you didn’t request this email, don’t fret, the security of your account has not been compromised. Somebody else must have requested your password. That’s exactly why we email it to you instead of just giving it out!
If Tom had been looking at his email inbox just then, he might have been able to cut off the cracker before he did any real damage. Unfortunately Tom wasn’t reading his email just then.